Circulating Light Beams
An Overview and Comparison by Dr. David Lewis Anderson
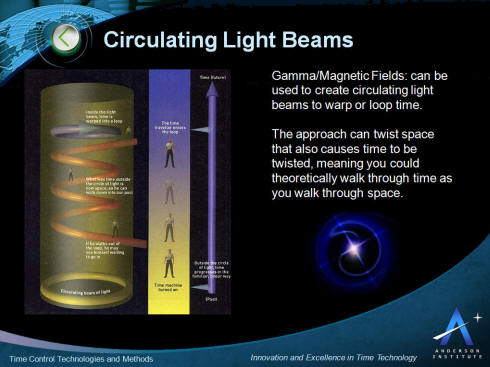
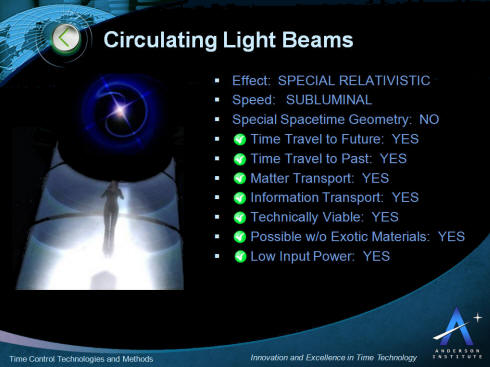
Circulating Light Beams can be created using gamma and magnetic fields to warp time. The approach can twist space that causes time to be twisted, meaning you could theoretically walk through time as you walk through space.
A number of interesting post-Newtonian phenomena are known to occur for rotating distributions of matter in Einstein’s general theory of relativity. Inertial frame dragging, for example, is a consequence of the weak gravitational field of a slowly rotating massive sphere. In addition, exact solutions of the Einstein field equations indicate the presence of closed timelike lines for rotating Kerr black holes, van Stockum rotating dust cylinders, and the rotating universe of Gödel.
The key characteristics of the application of circulating light beams for time control and time travel are presented in the picture below. This is followed by more detail describing the approach below.
Recently, Ronald L. Mallett solved the linearized Einstein field equations to obtain the gravitational field produced by the electromagnetic radiation of a unidirectional ring laser. It was shown that a massive spinning neutral particle at the center of the ring laser exhibited inertial frame dragging.
 Ronald L Mallett |
Mallett believes he has found a way to make it happen. By trapping light inside a photonic crystal, he can cause it to circulate. The energy of the circulating light will cause the space inside the circle to twist, causing a gravitational force.
This concept can be thought of as a spoon stirring a pot. The light is the spoon rotating around the inner rim of the pot. The space is the liquid being swirled by the spoon. As the space twists, it will coil the normally linear passage of time with it, spiraling the past, present, and future together into one continuous loop. It is this twisting of space and time that Mallett believes will make time travel possible.
Mallett and his partner at the University of Connecticut, Dr. Chandra Raychoudhuri, are seeking National Science Foundation funding for experiments that they hope will support their theories. Their first experiment will be to trap light in a crystal and observe the reaction of a neutron inside the circle.
 |
Dr. Mark Silverman at Trinity College in nearby Hartford has suggested a possible way to see evidence of time bending: Two identical samples of a radioactive substance would be prepared with identical half-lives. One would be introduced into the time machine circulating in the same direction as the light, the other in the opposite direction. If, at the end of the experiment, one sample had decayed further than the other, Mallett's theories of time travel would be supported.
 |
This is where the line between philosophy and physics seems to blur. "All of these things have their root in philosophy," says Mallett. But he explains that the difference between physics and philosophy is experiment. "All of these things would be philosophy without experimentation," he says. True, the parallel-universe theory has not been directly supported by experiment, but Mallett uses the Heisenberg Uncertainty Principle to explain
why the parallel universe theory is probable.
Heisenberg's Uncertainty Principle says that we cannot predict both the position of an electron and its spin at any given moment. Without this principle, "the universe should have collapsed immediately after it was formed," says Mallett. A hydrogen atom, one of the building blocks of our universe, consists of a proton and an electron. Since the proton and electron have opposite charges they should be attracted to each other, collide, and destroy the atom. But if that happened, we would know both the position of the electron (the point of impact with the proton) and its spin (none); therefore it is impossible for them to collide.
 Sun distorting spacetime. |
It has long been known(3, 4) that the van Stockum solution for the exterior metric of an infinitely long rotating dust cylinder contains closed timelike lines. Dr. Mallett has proposed that closed timelike curves also
occur for an infinitely long circulating cylinder of light. This model also shares some of the same limitations as the van Stockum solution in that the metric is not asymptotically flat, however, has emphasized that certain aspects of an infinitely long rotating dust cylinder may be shared by a long finite one. This may also apply to a long but finite circulating cylinder of light.












1 comment:
Talking style and communication needs always vary from person to person. So whichever you choose, the cost must be to cut down on the Telephony rates. Deregulation has opened up the wide arena and Internet Phone Service without any universal line charges or local taxes.
Post a Comment